OneForAll, A Powerful Chinese Subdomain Enumeration Tool
OneForAll is a Chinese recon tool for enumerating subdomains. Chances are you already use OWASP Amass as your primary subdomain enumeration tool; but unlike other instances of tool overlap, OneForAll is a practical supplement to provide an extra edge due to its Chinese context. OneForAll pulls from a multitude of exotic Chinese data sources that other tools typically do not query — FOFA, Baidu Cloud Observation, Gitee, and ChinaZ Alexa, to name a few in its vast collection. This improves your chances of finding unique, previously undiscovered entry points during your reconnaissance workflow.

In his Bounty Thursdays video, Stokfredrik highlights OneForAll:
{{< youtube id=“x9UFlxMz-po?start=108” >}}
Here’s a short list of all the different data points OneForAll pulls for your target:
- General checks: Basic enumeration of DNS records, zone transfer vulnerability, cross-domain policy, HTTPS certificate, content security policy, robots.txt, sitemap xml
- Bruteforce: “Subdomain blasting” via dictionary file and custom fuzzing, with support for batching and recursion
- DNS: BinaryEdge, BufferOver, CEBaidu, Chinaz, Circl, DNSDB, DNSDumpster, HackerTarget, IP138, IPv4Info, Netcraft, PassiveDNS, PTRarchive, Qianxun, RapidDNS, Riddler, Robtex, SecurityTrails, SiteDossier, Threatcrowd, WzPC, XimCX
- Certificate transparency: Censys, Certspotter, crt.sh, Entrust, Google, Spyse
- Web archives: Wayback Machine & Common Crawl
- Threat intelligence: Alienvault, RiskIQ, ThreatBook, ThreatKeeper, VirusTotal
- Search engines: Ask, Baidu, Bing, DuckDuckGo, Exalead, FOFA, Gitee, GitHub, Google, Shodan, So.com, Sogou, Yahoo, Yandex, Zoomeye
OneForAll’s documentation and source code comments are unfortunately in Chinese. Although a secondary English version of the README is available, many parts of the text are cryptic due to poor grammar. The below will provide some more helpful details on how to use OneForAll for the rest of us.
Installation
Check that your Python 3 environment meets the minimum versions required:
python3 -V
pip3 -V
python3 should be at least version 3.8.0 and pip3 at least version 19.2.2.
Clone the OneForAll project repository:
git clone https://github.com/shmilylty/OneForAll.git
As an optional step, make use of virtualenv to keep the install clean and separate from your system python environment:
virtualenv -p python3 .venv
source .venv/bin/activate
Install the required dependencies:
cd OneForAll
python3 -m pip install -U pip setuptools wheel
pip3 install -r requirements.txt
cd oneforall
python3 oneforall.py --help
Notice how you need to cd into the subfolder oneforall of the project directory. I’m not sure why the project is structured this way, but it is an annoying quirk when running the tool.
General Usage
Make sure you’re in the project subfolder oneforall (see note above), and execute the main python file with the run argument:
python3 oneforall.py --target <domain> run
The command line flags are verbose and redundant at times, such as having to specify run each time. Here are the optional flags for advanced usage:
--valid None
--brute True
--port <default | small | large>
--format <csv | tsv | json | yaml | html | xlsx >
--dns False
--req False
--takeover True
--show True
--path <output path>
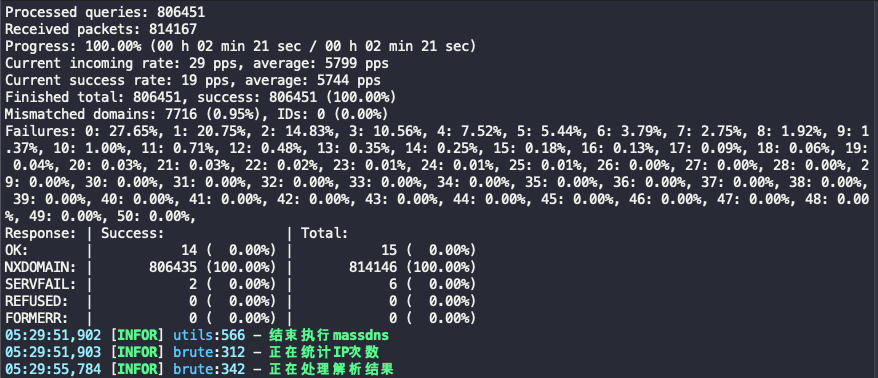
Brute Force Subdomain Blasting
A key feature of OneForAll is its module for brute force subdomain enumeration, enabled by the --brute True flag. The Chinese generally refer to this technique as “subdomain blasting”:
This module has both conventional dictionary blasting and custom fuzz mode. It supports batch blasting and recursive blasting, and automatically judges pan-parsing and processing.
The --word True flag enables brute force. Here are examples to configure the blast radius.
--word True --process 1
--word True --wordlist subnames.txt
--word True --recursive True --depth 2
--fuzz True --place m.*.d.com --rule '[a-z]'
A copy of MassDNS is included in the code repository to quickly resolve the list of domain names. OneForAll claims the tool can resolve at speeds up to 10,000 packets per second. However, the hardcoded nameservers are China-based, so for faster speeds you may overwrite this file with your own set of optimal DNS resolvers.
Checking for Subdomain Takeovers
Also nice is the built-in check for subdomain takeovers, which checks for a number of services including Heroku, Shopify, BitBucket, Azure, and more. Enable the check with the --takeover True flag.
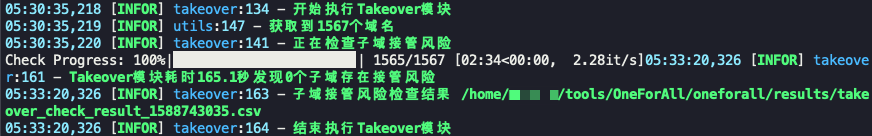
Check out the list of OneForAll’s takeover services in fingerprints.json, which you can edit to add your own custom fingerprints. EdOverflow maintains a more comprehensive list of potential services on GitHub at “Can I take over XYZ?”.
Export to Variety of Formats
OneForAll outputs to Excel format by default. Also supported are rst, csv, tsv, json, yaml, html, dbf, latex, and ods.
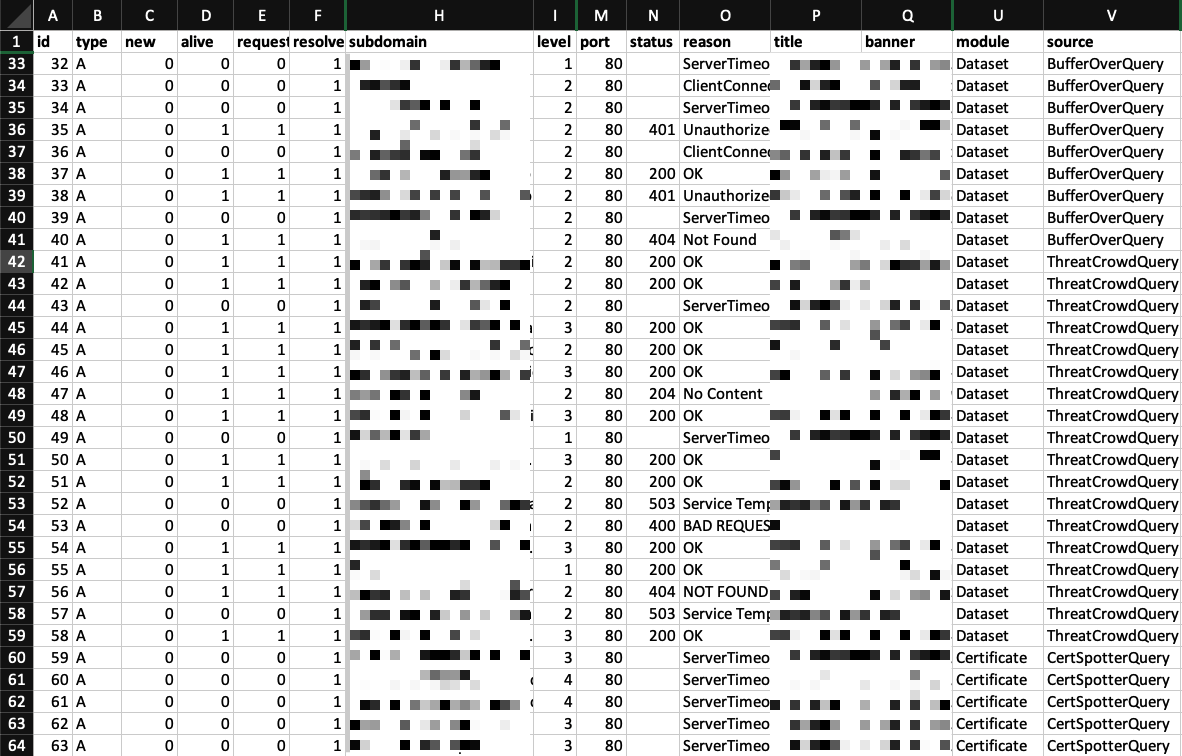
With each run, OneForAll updates a SQLite database file storing all your historical results.
Input Your API Keys
For the most comprehensive results, edit oneforall/api.py to add your API keys for the services below.
- Censys
- BinaryEdge
- Chinaz
- Bing
- SecurityTrails
- FOFA
- RiskIQ
- Shodan
- ThreatBook
- VirusTotal
- Zoomeye
- Spyse
- Circl
- DNSDB
- IPv4info
- Github
- PassiveDNS
Integrating Into Multi-Tool Recon Workflow
The variety of output options are nice (e.g. yaml, csv, xlsx), but each of the options are rich formats containing layers of metadata for each subdomain such as HTTP status code, banner, module used, data source. I prefer chaining specialized tools that do just one thing great, like httprobe and subjack as part of my recon workflow. So what if you just want a simple flat text file containing only the subdomains discovered?
One way to work around this without modifying the tool’s source code itself is to export as --format json, and then use jq to select the subdomains. Further, sed can clean up the extra quotes in each line, and sort -u can filter out duplicate data. See below for an example command chaining these:
cat <path to OneForAll results>/<target>.json | jq '.[].subdomain' | sed 's/\"//g' | sort -u > subdomains_oneforall.txt
Conclusion
Not only does OneForAll discover a target’s subdomains, but it also processes the results by making HTTP requests to probe for alive hosts and ports, and checking for subdomain takeovers on a variety of popular services.
First released in August 2019 by Jing Ling (shmilylty), OneForAll is still in early stages of active development. The project documentation states the developer’s aspiration to add additional modules that would make this even more of an “all in one” tool. To keep up with the latest features and bug fixes in OneForAll’s source code, sync your local version often:
git fetch --all
git reset --hard origin/master
git pull
From what I can tell, even without advanced configuration to optimize the runs, the execution is surprisingly quick and the quantity of results is comparable to what I would see from a basic run of amass enum. I am curious to run a quantified benchmark on speed and data quality between OneForAll and Amass for better comparison in the future.
The current state of OneForAll lacks the reliability to drop into a fully automated recon pipeline alongside a set of stable tools. The terminal output by default is verbose and noisy. Even from my limited testing, I would run the same command on a target multiple times, and sometimes the whole process would crash during the processing phase.
Because the project is in Chinese, it’s difficult to keep up with existing GitHub issues much less open up new ones.
Keep a close eye on the Chinese hacking community for unique insights and innovative techniques. There are all sorts of new data sources you can explore just by peeking into the inner workings of OneForAll.